Understanding the mechanism behind phone number lookups
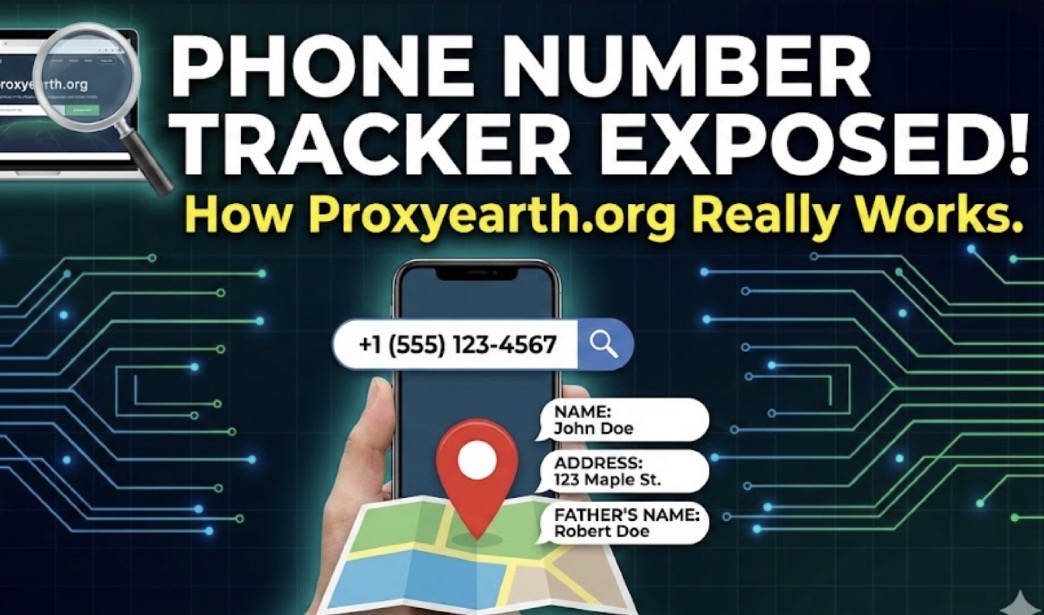
Websites that claim to provide a person’s name, address, and even “father’s name” just by entering a mobile number are rarely performing real-time tracking. Instead, they function as search engines for static, leaked data. Here is a breakdown of how they work and why they are able to show such specific personal details.
1. The Source: Leaked Administrative Databases
The specific combination of data fields you mentioned—Name, Address, and Father’s Name—is characteristic of Know Your Customer (KYC) forms used by telecommunication companies and government ID registries (such as CNIC databases in Pakistan or Aadhar-linked telecom data in India).
- Leak Origin: These sites usually operate by accessing large dumps of data that were stolen or leaked from telecom operators or third-party vendors years ago.
- Static vs. Live: The information is static. It reflects the data as it was when the leak occurred (e.g., 2018, 2020). If the person has moved house or changed their legal name since then, the website will display outdated information.
Preparing Your Link…
Click the button below to visit mobile number location tracker.
2. How the Lookup Works
When you enter a phone number into a site like Proxyearth, the backend process is relatively simple:
- Query: The website takes the phone number you entered and treats it as a search keyword.
- Database Scan: It scans its hosted database (often containing millions of rows of leaked user records) for a match.
- Retrieval: If the number exists in the leaked dataset, it pulls the associated row, which typically includes the subscriber’s full name, home address, ID number, and father’s name (a standard field in South Asian identity documents).
- Display: The site displays this text data to the user.
Crucial Distinction: This is not GPS tracking. The “address” shown is the billing or permanent address registered when the SIM card was bought, not the phone’s current physical location.
3. The “Truecaller” Difference
While apps like Truecaller rely on crowdsourced data (users sharing their contact lists), “SIM Database” sites rely on proprietary administrative data.
- Crowdsourced (Truecaller): Shows the name that other people have saved the number as (e.g., “John Plumber”).
- Leaked Database (Proxyearth type): Shows the official name on the government ID used to buy the SIM (e.g., “Johnathan A. Doe”).
4. Privacy and Security Risks
Using or relying on these websites carries significant risks:
- Data Brokerage: Many of these sites are free because they collect data on you while you use them. They may log your IP address and the numbers you search for, building a profile of your interests.
- Malware and Ads: These sites often operate in a legal grey area and are filled with invasive pop-up ads, redirect scripts, or potential malware downloads disguised as “Pro” tools.
- Inaccuracy: Because the data is from old leaks, it is frequently incorrect. A phone number might have been recycled and assigned to a new person, but the database still links it to the previous owner, leading to cases of mistaken identity.
- Illegality: Accessing or distributing citizens’ private data (PII) without consent is a crime in most jurisdictions.
Summary
Sites like Proxyearth do not “track” a phone in the way a spy movie depicts. They simply look up a number in a stolen phonebook. They cannot see where a person is standing right now, listen to calls, or read messages. They are archives of digital history—specifically, the history of data breaches.
For a deeper dive into how digital footprints and OSINT (Open Source Intelligence) tools are used to find information, you can watch this educational breakdown of the techniques involved.
OSINT tools to track you down. You cannot hide (these tools are wild)
This video explains the broader context of how investigators (and attackers) use data points like phone numbers to find information, helping you understand the importance of digital privacy.
OSINT tools to track you down. You cannot hide (these tools are wild) – YouTube